Have you ever noticed the strange string
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
inside Android logs, browser histories, or debugging tools?
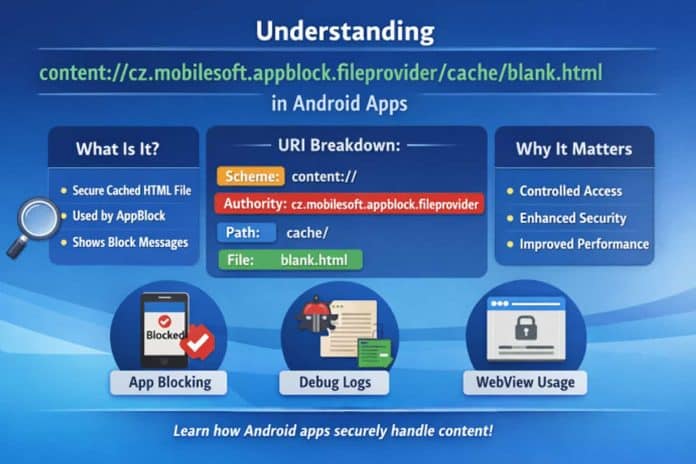
At first glance, it looks like a broken link or malware artifact. In reality, this URI is part of Android’s powerful secure content-sharing system and belongs to the popular productivity app AppBlock.
This guide explains what this URI really means, how Android FileProviders work, and why modern apps rely on content URIs instead of exposing real file paths.
Key Highlights
- The URI is a secure gateway to a cached HTML file used internally by AppBlock.
- Android Content URIs protect private app files from unauthorized access.
- AppBlock uses this file to display clean block messages instead of error pages.
- FileProvider improves security, performance, and privacy.
- Proper permission handling prevents data leaks and abuse.
What Are Android Content URIs?
Android no longer allows apps to freely share raw file paths. Instead, it uses content URIs, which act as secure references to data.
Rather than exposing:
/data/data/app/cache/file.html
Android safely shares:
content://authority/path/file
This system protects user data and enforces permissions.
Structure of the URI
General format:
content://<authority>/<folder>/<filename>
Breaking down:
- content:// → Content scheme
- cz.mobilesoft.appblock.fileprovider → AppBlock’s FileProvider
- cache → Cached directory
- blank.html → Placeholder web file
Why Content URIs Are More Secure
| Feature | File Path | Content URI |
| Visibility | Exposed | Hidden |
| Permissions | Broad | Granular |
| Sharing | Risky | Controlled |
| Revocation | No | Yes |
This design ensures that apps can share files without exposing their file system.
What Is AppBlock?
AppBlock is a productivity and digital wellness app by MobileSoft s.r.o. It helps users:
- Block distracting apps
- Restrict websites
- Improve focus and screen-time control
Why AppBlock Uses blank.html
The cached file blank.html serves multiple purposes:
- Displays block messages
- Prevents broken screens
- Loads instantly from cache
- Improves UX when content is restricted
Instead of errors, users see a clean placeholder.
FileProvider Setup Example
<provider
android:name=”androidx.core.content.FileProvider”
android:authorities=”cz.mobilesoft.appblock.fileprovider”
android:exported=”false”
android:grantUriPermissions=”true”>
<meta-data
android:name=”android.support.FILE_PROVIDER_PATHS”
android:resource=”@xml/file_paths” />
</provider>
Accessing the URI in Code
Uri uri = Uri.parse(“content://cz.mobilesoft.appblock.fileprovider/cache/blank.html”);
try (InputStream is = getContentResolver().openInputStream(uri)) {
BufferedReader br = new BufferedReader(new InputStreamReader(is));
StringBuilder data = new StringBuilder();
String line;
while ((line = br.readLine()) != null) {
data.append(line);
}
} catch (Exception e) {
Log.e(“AppBlock”, “Unable to load cached file”, e);
}
Where You’ll See This URI
1. While Using AppBlock
When a site/app is blocked, this file loads.
2. In System Logs
Appears during:
- WebView redirects
- Cache reads
- App restrictions
3. In WebView Apps
Used for:
- Offline placeholders
- Blocked content fallback
- Progressive loading
Security Best Practices
| Security Layer | Best Practice |
| Authority | Must be unique |
| Paths | Restrict shared folders |
| Permissions | Temporary only |
| Validation | Block path traversal |
Common Issues & Fixes
Permission Errors
getContentResolver().openFileDescriptor(uri, “r”);
WebView Not Loading
shouldInterceptRequest() → openInputStream()
Advanced Uses
Custom File Sharing
<paths>
<cache-path name=”cache” path=”.”/>
</paths>
Offline Web Support
- App shell
- Cached HTML
- Service workers
Performance Tips
| Cache Type | Benefit |
| Memory | Fastest |
| Disk | Larger |
| Hybrid | Best balance |
Use background threads, clean resources, and stream large files.
Final Thoughts
The URI
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
is not random—it is a perfect example of how modern Android apps handle data securely, efficiently, and intelligently.
By mastering Content URIs and FileProviders, developers can create safer, faster, and more professional mobile experiences.
FAQs
Is it dangerous?
No. It’s a secure internal file reference.
Can other apps read it?
Only with explicit permission.
Why is it in logs?
Because AppBlock loads it when blocking content.
Can I open it manually?
No—only the AppBlock app has access.